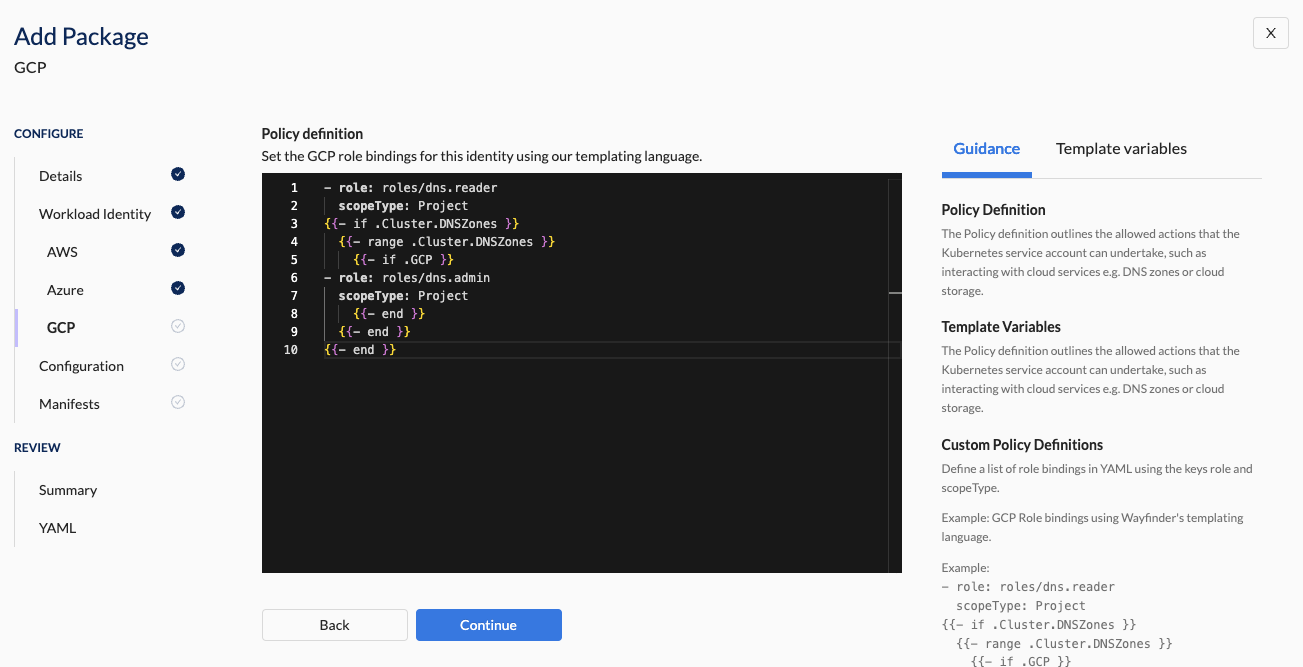
GCP Policy Definition
The policy definition outlines the actions that the Kubernetes service account is allowed to undertake in GCP when running on a GCP GKE cluster, such as interacting with cloud services like DNS zones or cloud storage.
Add your policy in the YAML generated by wf init package or prepare it using the Web Interface. See the CLI instructions section for details where you selected 'yes' when asked if your workload identity required cloud access.
Web Interface Instructions
Steps
- Use the text editor to define a policy. See example: GCP Role Bindings Template
- Use Wayfinder's Templating Language to make the policy specific for different environments or resources.
- Click the Continue button
Screenshot(s):
Properties
| Field | Description |
|---|---|
| Policy Definition | The YAML of the custom policy definition. Define a list of role bindings in YAML using the key's role and scopeType: - Role: name of a pre-defined (or self-managed) GCP role to use. - ScopeType: Project Note: 'Project' is currently the only supported scope type. See example template for reference. |
What comes next?
If the package requires cloud access to other Providers, then you need to configure the corresponding Policy Definition(s):
If your package doesn't require further cloud access configuration:
Related Reading
Examples
GCP Workload Identity Role Bindings Template
- role: roles/dns.reader
scopeType: Project
{{- if .Cluster.DNSZones }}
{{- range .Cluster.DNSZones }}
{{- if .GCP }}
- role: roles/dns.admin
scopeType: Project
{{- end }}
{{- end }}
{{- end }}